All Posts in Peringatan Keamanan

Multiple Flaws Found in Ninja Forms Plugin Leave 800,000 Sites Vulnerable
By Admin in Peringatan Keamanan at August 01, 2023
Multiple security vulnerabilities have been disclosed in the Ninja Forms plugin for WordPress that could be exploited by threat actors to escalate privileges and steal sensitive data.The flaws, tracke...
Read more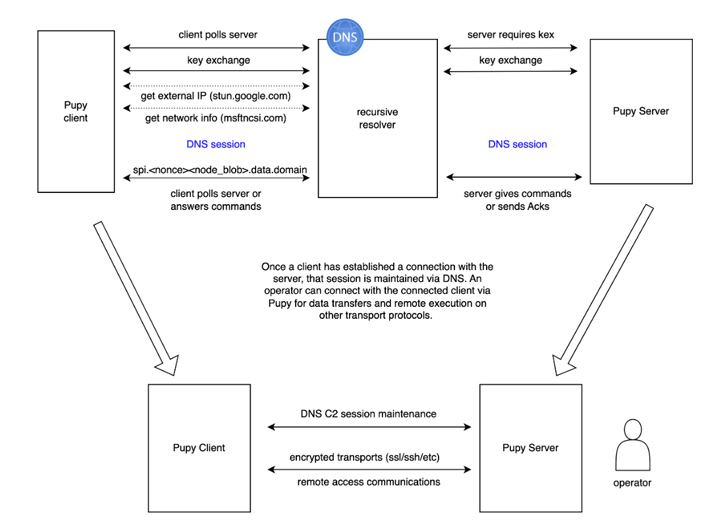
Decoy Dog: New Breed of Malware Posing Serious Threats to Enterprise Networks
By Admin at July 28, 2023
A deeper analysis of a recently discovered malware called Decoy Dog has revealed that it's a significant upgrade over the Pupy RAT, an open-source remote access trojan it's modeled on."Decoy Dog has a...
Read More
Critical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking
By Admin at July 26, 2023
A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors to execute arbitrary code and seize full control of vulnerable devices.Cataloged as CVE-2...
Read More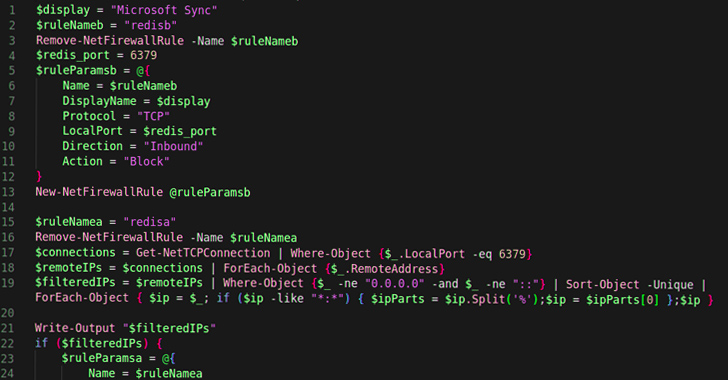
New P2PInfect Worm Targeting Redis Servers on Linux and Windows Systems
By Admin at July 24, 2023
Cybersecurity researchers have uncovered a new cloud targeting, peer-to-peer (P2P) worm called P2PInfect that targets vulnerable Redis instances for follow-on exploitation."P2PInfect exploits Redis se...
Read More
New OpenSSH Vulnerability Exposes Linux Systems to Remote Command Injection
By Admin at July 24, 2023
Details have emerged about a now-patched flaw in OpenSSH that could be potentially exploited to run arbitrary commands remotely on compromised hosts under specific conditions."This vulnerability allow...
Read More
Zimbra has warned of a critical zero-day security flaw in its email software that has come under active exploitation
By Admin at July 20, 2023
"A security vulnerability in Zimbra Collaboration Suite Version 8.8.15 that could potentially impact the confidentiality and integrity of your data has surfaced," the company said in an advisory.It al...
Read More
Malicious USB Drives Targetinging Global Targets with SOGU and SNOWYDRIVE Malware
By Admin at July 18, 2023
Cyber attacks using infected USB infection drives as an initial access vector have witnessed a three-fold increase in the first half of 2023, That's according to new findings from Mandiant, which...
Read More